Playing the Long Game: Why Your Sock Puppet Might Be the Only Thing Standing Between You and your Target File
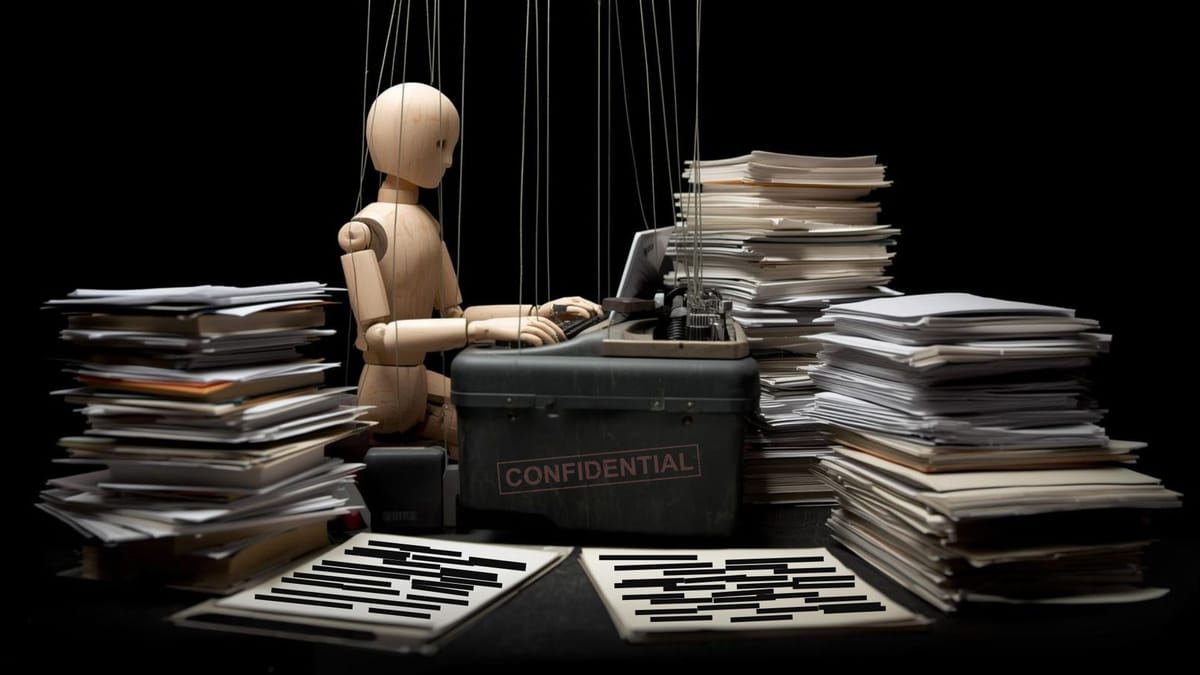
I never set out to become an investigative journalist. That's the funny thing about this line of work - nobody really plans on becoming the kind of person who spends their evenings cross-referencing FOIA responses with metadata scraped from leaked databases while wondering if the sedan that's been parked across the street for three days is just a coincidence.
But here we are.
If you're reading this, chances are you're either already in the game or you're standing at the edge, wondering if it's worth stepping in. Maybe you're a seasoned OSINT researcher who's been running sock puppets since before Twitter became X. Maybe you're a citizen journalist who just realized that the local PD's surveillance program isn't quite as "constitutional" as they claim. Or maybe you're just someone who's finally had enough of the gaslighting, the stonewalling, and the casual assumption that they get to operate in the shadows while we have to operate in the light.
Either way, you need to understand something fundamental: the system is designed to identify, track, and neutralize anyone who tries to hold it accountable. And if you're going to survive in this space, you need to be smarter than the people who wrote the rules.
This isn't about paranoia. This is about tradecraft.
The Legitimacy Trap
Let's start with the question nobody wants to ask out loud: Is using a sock puppet account to investigate government misconduct actually legal?
The short answer is: mostly, yes - but with asterisks the size of freight trains.
The law, as it exists on paper, is surprisingly permissive. Federal statutes like 5 U.S.C. § 552 (the Freedom of Information Act) don't require you to provide your legal name when requesting records. You can file as "Concerned Citizen," "John Q. Public," or "FuckTheSystem69" if you want. The statute says "any person" can request records. It doesn't define "person" as requiring government-issued ID verification.
Sock puppet accounts - pseudonymous identities used for research, investigation, and information gathering - occupy a similar legal gray zone. Creating a fake account on Twitter or Facebook violates their Terms of Service, sure. But violating a TOS isn't a crime. It's a contract dispute. They can ban you. They can't arrest you.
Unless.
Unless you're using that sock puppet to commit fraud. Unless you're impersonating a specific real person to deceive others. Unless you're using it to harass, stalk, or threaten. Unless you're deploying it in a way that crosses the line into Wire Fraud (18 U.S.C. § 1343), False Statements (18 U.S.C. § 1001), or Computer Fraud and Abuse Act violations.
And here's the kicker: the line is wherever they say it is.
The Two-Tiered System of "Proper Authorization"
When you dig into the literature on sock puppet accounts - the whitepapers, the legal analyses, the risk assessments - you'll keep running into this phrase: "proper authorization."
Law enforcement can use sock puppets. Intelligence agencies can use sock puppets. Corporate security teams can use sock puppets. They all operate under "proper authorization."
But what the fuck does that actually mean?
For a federal agent, "proper authorization" means operating under the legal authority of their agency, with oversight from DOJ, Congress, or the FISA court (depending on the operation). Their authorization comes from inside the system. It's granted by the very institutions they're supposed to be accountable to.
For you - a citizen, a journalist, an independent researcher - "proper authorization" means... what, exactly?
Are you supposed to go ask the FBI for permission to investigate the FBI? Are you supposed to file a form with your local PD before you start documenting their pattern of illegal stops? Should you check with the NSA before you start mapping their domestic surveillance infrastructure?
This is the trap.
The concept of "proper authorization" creates a legal and ethical monopoly on investigative work. It defines legitimate investigation as something only sanctioned institutions can do. Everyone else is an amateur, a vigilante, a troublemaker.
But here's the thing they don't want you to realize: You don't need their permission.
Your authorization comes from the First Amendment. Your authorization comes from the fundamental principles protected by the founding documents of our Republic, and we are not a "democracy" - there are fundamental differences between the two and "they" have muddied those waters with malicious intent for years. The government is accountable to We The People, not the other way around. Your authorization comes from the fact that power, left unchecked, will abuse its authority every single time, and we're seeing that play out in real-time.
You are self-authorized to investigate them. YOU are the ultimate authority from which all else is derived. Step onto this stage in and with total confidence.
The Retaliation Playbook
Let's talk about what happens when you start poking around.
I'm not talking about casual inquiries. I'm talking about the moment you go from being a curious citizen to being a problem. The moment your FOIA requests start targeting specific programs, specific agents, specific incidents that someone higher up the chain would prefer stayed buried.
The system has a playbook for dealing with people like us. It's been refined over decades, tested on activists, journalists, whistle-blowers, and anyone else who's ever had the audacity to ask uncomfortable questions.
Stage One: Slow-Walking and Stonewalling
Your FOIA request gets acknowledged. Then it sits. And sits. And sits. You get periodic updates: "Still processing." "Consulting with other agencies." "Estimating scope." Months turn into years. The documents you requested - if they ever arrive - are so heavily redacted they're useless. Entire pages are just black bars. You appeal. The appeal gets denied. You file a new request with slightly different language. The cycle repeats.
This isn't bureaucratic inefficiency. This is a feature, not a bug. The goal is to exhaust you. To make the process so painful, so expensive, so time-consuming that you give up.
Stage Two: Soft Retaliation
If you persist, things start to get weird.
Maybe you get flagged for "enhanced screening" by TSA. Not a no-fly list - nothing that dramatic - just random additional searches every single time you fly. Maybe the IRS decides this is the year to audit you. Maybe your professional licensing board suddenly has questions about your credentials. Maybe your bank starts filing Suspicious Activity Reports on your transactions.
These are all plausibly deniable. Each one, taken individually, could be a coincidence. But taken together? It's a message.
The message is: We know who you are. We know where to apply pressure. Back off.
Stage Three: Direct Confrontation
If you're still not getting the hint, they'll come talk to you.
Two agents show up at your door. They're polite. They're professional. They just want to ask a few questions about your "research interests." They mention things they shouldn't know - who you've been talking to, what you've been searching for online, where you were last Tuesday. They don't threaten you directly. They don't need to. The threat is implicit: We're watching. We can make your life very difficult. Are you sure you want to continue?
This is where most people fold.
Stage Four: Prosecution
If you don't fold, they'll find something. And I mean that literally - they will find something to charge you with.
Maybe it's a process crime. You made a false statement to a federal agent during that "friendly" interview (even if you didn't). Maybe it's obstruction. Maybe it's a CFAA violation because you accessed a public website in a way that technically violated the TOS. Maybe they use parallel construction - intelligence gathered through classified surveillance programs, then laundered through "traditional" investigation to build a prosecutable case.
The goal isn't necessarily to convict you. The goal is to destroy you financially and professionally through the process itself. Legal defense costs hundreds of thousands of dollars. Your reputation gets shredded. Your family suffers. Even if you're acquitted, you're broken.
This is the cost of asking questions they don't want answered.
The FOIA Honeypot
Here's the part that's going to piss you off: The FOIA process itself is a surveillance mechanism.
Think about it. Every time you file a FOIA request, you're telling the government:
- What you're interested in
- What you know (or suspect)
- When you're actively investigating
- Where to send the response (creating a trail back to you)
Even if you file under a pseudonym, even if you use a mail forwarding service, you've still raised your hand. You've identified yourself as someone worth watching.
The agencies have entire divisions dedicated to analyzing FOIA requests. They profile requesters. They cross-reference requests against ongoing investigations, litigation, activist groups, media inquiries. They're looking for patterns.
If you file a FOIA about, say, the illegal use of confidential informants to deploy malware, they're going to ask themselves: Why does this person know enough to ask this specific question?
Are you a target of that program? Are you a whistle-blower? Are you a journalist who's been talking to sources inside? Are you a lawyer building a case?
They don't need to know your real name to start investigating you. They just need to know you're a threat.
Building a Legal Fiction: The Pseudonym Strategy; aka "Sock Puppets
So how do you navigate this minefield without getting blown up?
You build a legal fiction.
I'm not talking about identity theft or fraud. I'm talking about constructing a legitimate pseudonymous identity with actual legal backing. Something that can withstand scrutiny without exposing you to prosecution.
Here's the framework:
Step One: The Affidavit
Get an "Affidavit of One and the Same" notarized. This is a legal document stating that [Your Legal Name] and [Your Pseudonym] are the same person. Courts recognize this all the time - actors, writers, musicians use stage names and pen names with legal force.
This affidavit serves two purposes:
- It establishes the legal legitimacy of your pseudonym
- It creates documented proof (for yourself) if you ever need to verify identity
Critical: Don't file this affidavit anywhere public. Don't record it with the county clerk. Keep the original in a safe place. It exists as insurance, not as public record.
Step Two: The Infrastructure
Once you have the affidavit, you build the supporting infrastructure:
- Mail forwarding service: Register it under the pseudonym. Pay with crypto or cash if possible. This gives you a physical address that isn't your home.
- Email account: Create it under the pseudonym. Use ProtonMail, Tutanota, or another service with strong privacy protections.
- Website/blog: This is crucial for establishing journalist credentials. It doesn't need to be fancy. It just needs to show a body of work - articles, investigations, commentary. This is what you'll cite when requesting FOIA fee waivers.
- Financial separation: If possible, set up payment methods (prepaid cards, crypto wallets) that aren't tied to your legal name.
Step Three: Establish Journalist Credentials
This is where a Ghost blog or another platform becomes essential.
The FOIA statute allows fee waivers for requests that serve the public interest, including journalism. You don't need to work for the Washington Post. Freelance journalists, independent reporters, citizen journalists - they all qualify.
But you need to demonstrate that you're a journalist. That means:
- Publishing articles on matters of public interest
- Showing a pattern of investigative work
- Building a credible portfolio under your pseudonym
The goal: When you file a FOIA as [Pseudonym] and request a fee waiver citing journalist status, they evaluate the request based on the work, not the name. If your Ghost blog shows consistent, credible journalism, the waiver gets granted.
Step Four: Operational Security
None of this matters if you fuck up the OPSEC.
- Never cross the streams. Don't access your pseudonym accounts from your home IP. Use a VPN. Use Tor. Use public wifi. Create separation.
- Watch your writing style. If you've filed FOIAs under your legal name before, and now you're filing under the pseudonym, they can run linguistic analysis to match patterns. Vary your phrasing. Use AI to reword requests if needed.
- Minimize the paper trail. Don't produce the affidavit or POA unless absolutely required. The fewer documents connecting the two identities, the better.
- Assume compromise. Plan for the possibility that they'll figure it out eventually. What's your contingency? What's your legal defense? What's your exit strategy?
The FOIA Farm Alternative
If building a full pseudonymous identity sounds like too much work (or too much risk), there's another option: use a FOIA intermediary.
Organizations like MuckRock, the Electronic Frontier Foundation, and various FOIA-focused nonprofits file thousands of requests on behalf of clients, journalists, and the public interest. You pay them a fee (or they take your case pro bono), they file the request under their name, and the government sees the organization - not you.
The advantages:
- Your name never appears on the request
- Your specific inquiry gets buried in the volume of their other requests
- They have lawyers if the agency pushes back or retaliates
- Payment can sometimes be made anonymously
The disadvantages:
- You're not controlling the process directly
- They might decline requests that seem too risky or don't fit their mission
- There's still a trust element - they're receiving the documents first
The real value: Even if they figure out the FOIA came through MuckRock, they don't necessarily know who the ultimate beneficiary is. It could be a journalist, a lawyer, an activist, or you. The ambiguity creates space.
The Meta-Problem: Is Any of This Even Worth It?
Here's the question that keeps me up at night: Are we just playing a rigged game?
The FOIA process was supposed to be a transparency mechanism. It was supposed to give citizens oversight over their government. But in practice, it's been weaponized into a surveillance tool and a bureaucratic stalling tactic.
Even if you get the documents, they're redacted into meaninglessness. Even if you build the perfect pseudonym, they can still figure out who you are if they dedicate enough resources. Even if you do everything right, they can still retaliate in ways that are plausibly deniable and legally untouchable.
So why bother?
Because the alternative is surrender.
Because every FOIA request - even the denied ones, even the slow-walked ones - creates a record that the question was asked. Because every investigation - even the incomplete ones - chips away at the mythology of unaccountable power. Because every person who refuses to be intimidated makes it harder for them to intimidate the next person.
This isn't about winning in the traditional sense. This is about making them work for it, and exposing their mistakes like a hacker who just discovered an O-Day!
If they want to surveil us, we make them expend resources. If they want to intimidate us, we document it and publish it. If they want to prosecute us, we force them to do it in open court where their methods get exposed.
We play the long game. We build resilience. We share knowledge. We protect each other.
The Trade-Offs and the Reality Check
I'm not going to bullshit you: using sock puppets and pseudonymous identities for investigative work is risky.
You're operating in a legal gray zone where the rules are selectively enforced. What's considered "legitimate journalism" when the New York Times does it might be labeled "fraud" or "impersonation" when you do it. The system protects institutional actors and punishes outsiders.
Even if you do everything legally, you're still vulnerable:
- Platform bans: Twitter, Facebook, Reddit - they all have sock puppet detection algorithms. One slip-up and your account gets nuked, along with all the research and connections you've built.
- Legal retaliation: Even if they can't prove you did anything illegal, they can sue you into oblivion. Defamation suits, tortious interference, harassment claims - the process is the punishment.
- Personal costs: This work is exhausting. It's isolating. It strains relationships. It makes you paranoid (even when the paranoia is justified). You need to decide if you're built for this. Hunter S. Thompson once said, "There's no such thing as paranoia; it's always much worse than you think." It'd be funnier if it wasn't so true.
Before you jump in, ask yourself:
- Do I have the technical skills to maintain operational security?
- Do I have the financial resources to sustain a legal fight if it comes to that?
- Do I have a support network of people who understand this work?
- Do I have an exit strategy if things go sideways?
If the answer to any of these is "no," think hard about whether you're ready.
The Ethical Lines (And Why They Matter)
Here's where I'm going to sound like a hypocrite: even in this dirty game, there are lines you don't cross.
- Don't impersonate real people. Create fictional personas, sure. But don't steal someone's actual identity. That's not investigative journalism - that's identity theft.
- Don't harass or dox. The fact that they do it to us doesn't justify us doing it to them. There's a difference between exposing misconduct and ruining someone's life because you can.
- Don't fabricate evidence. Document what's actually there. The truth is damning enough without needing to manufacture it, and "they" will give you a mountain of it without even breaking a sweat.
- Don't endanger others. If your investigation puts sources, bystanders, or family members at risk, you need to rethink your methods.
Why does this matter? Because the moment you cross these lines, you give them everything they need to destroy you. And more importantly, you become the thing you're fighting against.
The entire justification for this work - the moral authority that lets us sleep at night - rests on the fact that we're exposing actual wrongdoing using methods that, while aggressive, don't involve the kinds of abuses we're documenting.
Lose that, and you're just another bad actor in a system full of them.
What They Don't Want You to Know
The most dangerous thing you can understand about this system is that it's not as powerful as it pretends to be.
Yes, they have resources. Yes, they have legal authority. Yes, they have surveillance capabilities that would make Orwell weep.
But they also have constraints:
- Limited bandwidth: They can't investigate everyone. They prioritize threats based on impact and visibility.
- Legal exposure: Every time they retaliate, they create evidence. Every time they overreach, they risk exposure.
- Internal dysfunction: These agencies are bureaucracies. They're plagued by turf wars, incompetence, and ass-covering. They're not the omniscient panopticon they want you to believe they are.
- Public scrutiny: The more people doing this work, the harder it is to target any single person without drawing attention.
The system relies on you being afraid. It relies on you self-censoring. It relies on you believing that resistance is futile.
The moment you stop being afraid, you become dangerous. And with the state of things nowadays, an army of dangerous citizens is EXACTLY what is needed. It's time to "shake the tree."
The Path Forward
If you're still reading this, you're either already in the game or you're about to be.
Here's what I'd tell you if we were having this conversation over a drink in a bar where nobody knows our names:
Start small. Don't go after the NSA on your first FOIA. Cut your teeth on local government - police records, city council emails, public works contracts. Learn the process. Build your skills. Make your mistakes when the stakes are lower.
Build your network. Find other people doing this work. Share resources. Share knowledge. Share threat intelligence. You can't do this alone.
Document everything. Every interaction with government agencies. Every weird thing that happens, and there WILL be weirdness! Every threat, implicit or explicit. Create a record. Publish it. Make it expensive for them to fuck with you. They'd rather guard their tactics than risk exposing them, rendering them ineffective for later use on someone else.
Take care of yourself. This work will grind you down if you let it. Set boundaries. Take breaks. Find meaning outside of the fight. You're no good to anyone if you burn out.
Remember why you're doing this. Not for glory (there isn't any). Not for money (there definitely isn't any). You're doing this because someone has to. Because the alternative is a world where power operates in total darkness and accountability is a fairy tale. THAT'S the world we live in NOW - the "files" release with zero accountability afterwards proved that already. Which circles us back into that "army of citizens" thing I mentioned earlier. It's a government FOR the people, not a people FOR the government. It's high time we step up. You know what they say: "If you want something done right, do it yourself."
The Final Word
I can't tell you what the right choice is. I can't tell you whether the risk is worth it. That's a decision you have to make based on your own circumstances, your own risk tolerance, your own moral compass.
What I can tell you is this: the people who are supposed to be holding the government accountable - the mainstream press, the courts, the elected officials - are failing and failing horribly. Some of them are captured. Some of them are complicit. Some get "Kirked" if they're too effective, and some of them are just too scared to do their jobs.
That leaves us. The obsessives. The cranks. The people who can't let it go even when we should because once you've got nothing else to lose you can't afford NOT to become dangerous.
When "they" have you backed into a corner just remind yourself: Cornered animals bite.
We're not heroes. We're not martyrs. We're just people who decided that the truth matters and uncovering hidden facts is the right thing to do.
And if that makes us dangerous, good.
They should be afraid of us. Because we're not going anywhere.
Long live the Republic.
If you found this useful, share it. If you think I'm full of shit, tell me why. If you're doing this work and you need to talk to someone who gets it, you know where to find me.
Stay safe. Stay smart. Stay angry.

